The US Department of Defense began notifying tens of thousands of people of their sensitive information in an email data breach last year.
oh TechCrunch In a security breach notification letter sent to victims on February 1 of this year, the Defense Intelligence Agency, the military intelligence arm of the Department of Defense, pointed out that between February “a number of emails were inadvertently exposed on the Internet by the service provider”. 3 and February 20, 2023.
read more:
Leak of sensitive emails
- As stated therein TechCrunchLetters about the disclosed breach relate to an email server located in an unsecured US government cloud that leaked sensitive messages to the Internet.
- An email server targeted at government customers is hosted in the Microsoft cloud;
- It got passwordless access, probably due to misconfiguration;
- The Department of Defense is sending these letters to about 20,600 victims.
“As a matter of practice and operational security, we do not comment on the state of our networks and systems. The affected server was identified and removed from public access on February 20, 2023, and the vendor resolved the issues caused by the exposure,” said Defense Department spokesperson CDR. An email was sent to Tim Gorman TechCrunch.
“DOD continues to collaborate with service providers to prevent and detect cyber incidents. The notification for the affected persons is continuing,” he said.
In total, about 3 TB of domestic military emails were leaked a year ago, some of which were related to the US Special Operations Command, known as SOCOM, which is responsible for US special military operations.
Some of the exposed information included sensitive personal information and questionnaires taken by potential federal employees seeking security clearances.
Anyone exposed to the email server's public IP can access sensitive data from any browser.
Security researcher Anurag Sen discovered and searched for the exposed data TechCrunch, which activated SOCOM on February 19. A day later, the server was brought to safety TechCrunch Propaganda the problem to senior US government officials.
According to the portal, it is not clear why the US Department of Defense took a year to investigate the incident or notify the victims. When contacted by the website, a Microsoft spokesperson declined to comment on the case.

“Internet evangelist. Writer. Hardcore alcoholaholic. Tv lover. Extreme reader. Coffee junkie. Falls down a lot.”



:strip_icc()/s02.video.glbimg.com/x720/12553381.jpg)

More Stories
Tornado in US: Drone images show destruction caused by event in Nebraska; Watch the video the world
FourFourTwo Magazine from the United Kingdom picks Flamengo as the Brazilian club with the best base
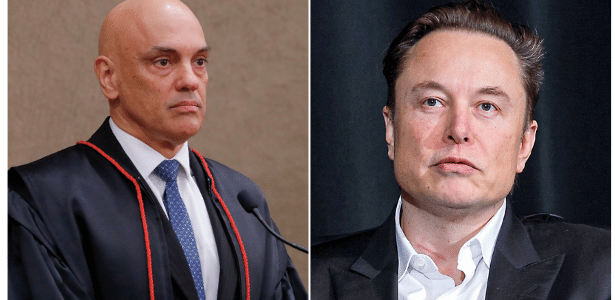
Brazilians demonstrate in London against Alexandre de Moraes